With the new year come new beginnings. Here is the first in our series of regular updates on new product capabilities. The periodic update will focus on the new capabilities added during each release.
Introduction to Appaegis IAC
Since this is our first of many updates, here is a recap of our product. Appaegis IAC is a cloud-based solution for secure access to applications and data using Zero Trust principles. Security teams benefit from
- Data specific policy enforcement controls to provide data loss prevention
- Continuous user activity reporting
- Ability to audit user access to a broad set of applications including Web, SSH, RDP and Kubernetes.
Key enhancements:
Appaegis follows an agile development and continuous deployment methodology. So here is a recap of the features released over the since December 2021 along with a sampling of screenshots to illustrate the capabilities.
The most recent features can be classified into the following categories:
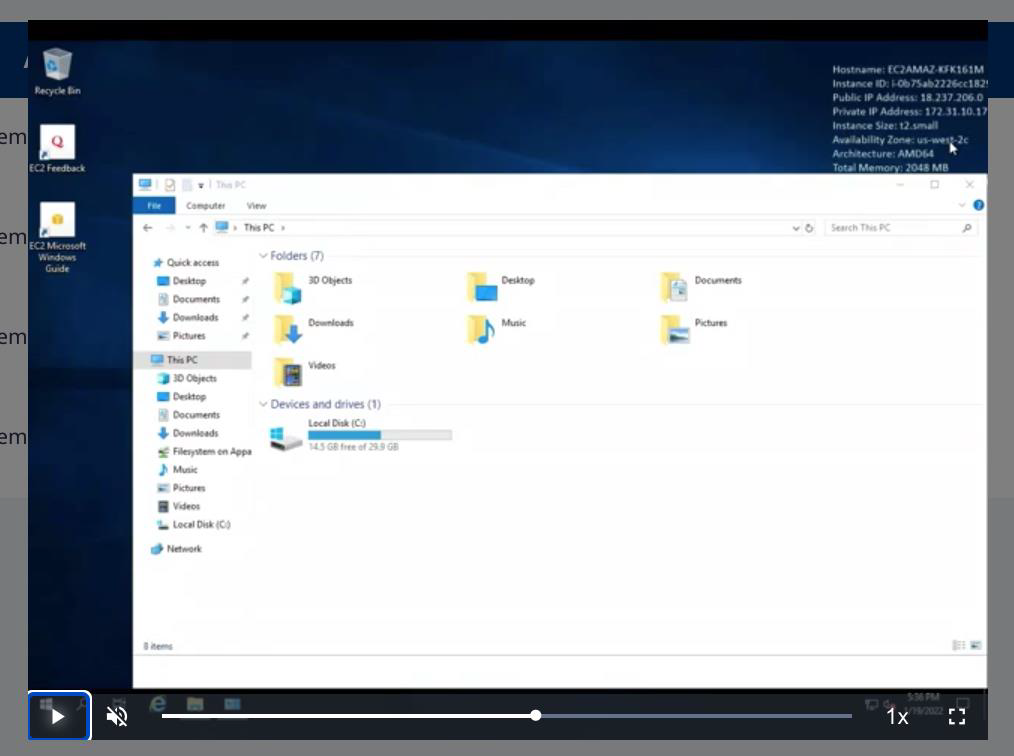
- Session recording:
Appaegis records SSH and RDP sessions and stores the recordings in secure storage. Recordings can be viewed at any time by authorized administrators. Recording of sessions are enabled on-demand and per application. Session recordings can be helpful for:
- User access audit
- Compliance reporting
- Sensitive data inspection:
Appaegis provides a solution for data inspection and sensitive data access detection.
- Web: Always on SSL/TLS decryption provides continuous visibility of sensitive data access
- SSH: SSH inspection applies deep file inspection of upload and download transfers
- RDP: RDP inspection applies deep file inspection of upload and download transfers

- Azure and HCP Key vault integrations:
Integration with key vaults allows strict enforcement of access control for groups using SSH to access critical platforms and applications. Those teams can consist of developers, network operations or partners and contractors that need remote access. Appaegis’ integration with multiple key management systems ensures that we can work with any customer environment.
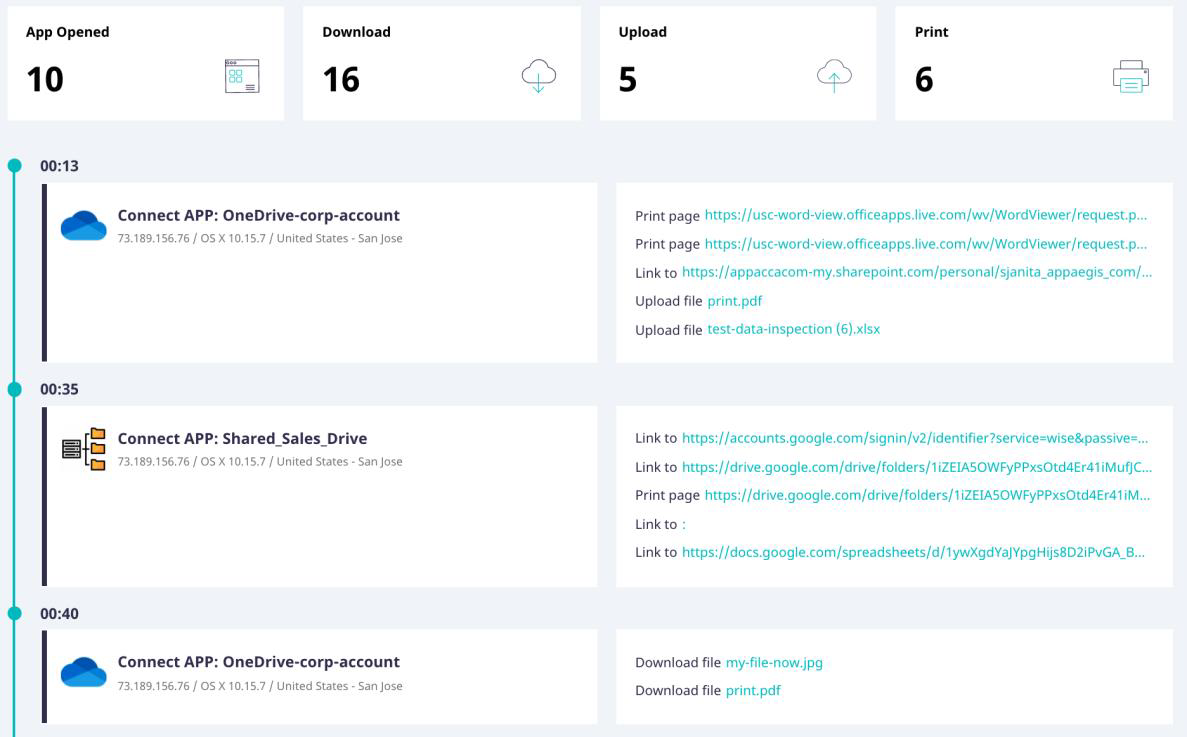
- Detailed user activity logging:
Appaegis provides detailed user activity down to the click and command level when a user access an application. Our continuous monitoring and logging provides real-time visibility, the keystone for security.
- Kubernetes activity logging:
Administrative commands executed on a Kubernetes cluster can be logged for visibility and analysis.

Watch for my next update in February!