
How to Make Data Central to Zero Trust
I had talked about Zero Trust in our previous blog. One of the key elements I discussed was the ability to ensure data security. According to the NSA “the fundamental purpose of Zero Trust is to understand and control how users, processes, and devices engage with data.” I can add on to every existing cliche about how data is the new currency. Instead, I will focus on discussing data security, assuming you agree that protecting data is important.
Here are the central tenants of zero trust solution that provides data centric security
- Address corporate applications, cloud workloads, SaaS and domination of web-based applications
In an application centric world, applications are the gateway to data. Protecting data requires protecting the pathway to applications and adhering to the principles of least privilege access. The fact that 50% of data breaches originate at the web application layer2 illustrates the importance of protecting application and data access.
According to Flexera1, 92 percent of enterprises have a multi-cloud strategy and 80 percent have a hybrid cloud strategy. According to Gartner the SaaS market is going to grow at a 20% CAGR between 2020 and 2022. The growth in market size is a measure of the rapid and growing adoption of SaaS.
This implies that any security strategy that ignores cloud services and SaaS, is destined for failure. Furthermore, the approach must cover all types of applications - internal and external. It must address all types of data - personal data, intellectual property, or any other data governed by regulator mandates.
The solution should also be able to provide granular context-based controls on operations performed on the data. Should the user be able to download the data, copy the data, print the data? Key safeguards required to ensure data security across applications.
The advent of the cloud era, distributed nature of data and applications, and growth in SaaS applications means that the traditional definition of a “network” no longer applies. A solution that provides secure or zero trust network access might not address the demands of a data centric world. The solution should be designed to be application and data centric.
- Threats are evolving and wishing them away is not an option
If this is not the understatement of the century, it is at least the understatement of the decade. Traditional signature-based methods are effective in addressing known threat patterns. Security strategies that include URL filtering to prevent unauthorized access are an essential component of every security architecture, but not sufficient. Implementing zero trust must include real-time detection of zero-day threats and prevention of data loss.
Detection of zero-day threats requires a combination of baselining, anomaly detection, auto discovery and machine learning. The combination can quickly detect new threats and importantly serve as a mechanism for data loss or data misuse prevention. Detection, real-time prevention, and defense against malicious actors is critical.
However, no security mechanism can guarantee 100% success. In order to troubleshoot instances of malicious activity, it is important that organizations maintain continuous and granular visibility into every interaction. Logs of these interactions are critical to post-incident analysis and essential for machine learning algorithms to get smarter.
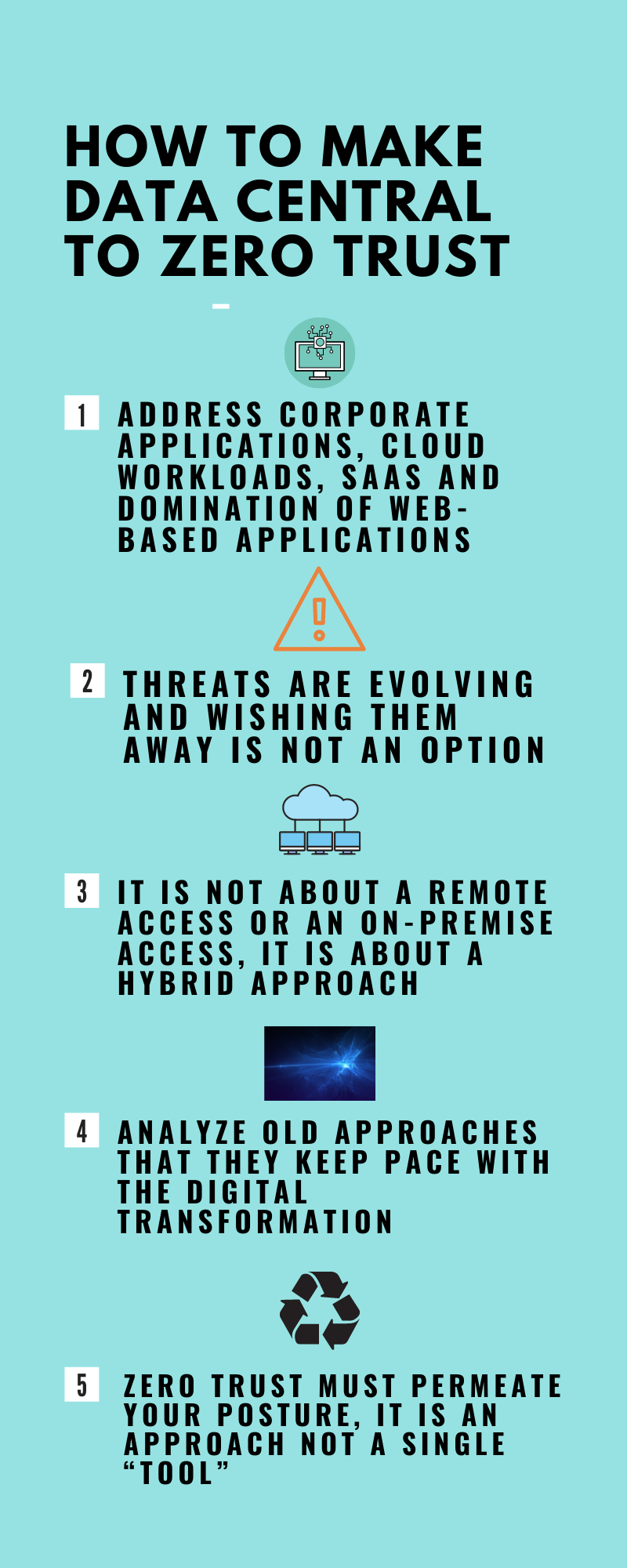
- It is not about a remote access or an on-premise access, it is about a hybrid approach
Remote work has skyrocketed. The new “normal” (if there is such a thing) is one where remote work and “on premises” work will coexist. Just as data centers and cloud-based deployments are going to coexist. Therefore, security solutions put in place must address both scenarios. “Addressing” in this context has several components.
The security solution must not require users to be retrained on using existing applications. The false fallacy that one must choose between robust security and better user experience can be debunked with existing technology. To the extent possible, user experience in accessing applications should stay similar regardless of location, network, managed or unmanaged device, for data center, cloud or SaaS applications.
The security solution should minimize the need to deploy and manage additional agents. The solution in place should provide granular visibility required for organizations to monitor transactions between end hosts, applications and data. Access that encrypts the exchange between users and applications, should not become a conduit for lateral movement of malware.
The solution deployed should protect data whether users are accessing the applications and data from their desktop, laptop or mobile device. The solution should ensure protection whether the device connects through the corporate network, from a trusted or untrusted network. In addition to delivering on the promise of data security, the solution must ensure a consistent and seamless user experience.
- Analyze old approaches that they keep pace with the digital transformation
Overburdened and understaffed security organizations are challenged with identifying and implementing solutions designed for a cloud first organization. One where cloud computing is not something that might happen in the future, but something that is a reality now.
Legacy solutions were not designed for a world where web browsers are the window to everything, or where SaaS is ubiquitous. Continuing to use legacy solutions alone (like VPNs), built for a network centric world, no longer provide the data security needed.
- Zero Trust must permeate your posture, it is an approach not a single “tool”
Zero Trust incorporates a strategic approach to security. At the crux of this approach is ensuring that access to data or applications has the required authorization. There is no implicit trust in any particular device or user. To be successful this approach must permeate all aspects of security.
Every tool must adhere to these principles. Note that awareness and training of the workforce must be an integral part of every organization's security strategy. Of course, one can find a never-ending list of requirements to harden the trust architecture required to ensure data security.
The fact that zero trust is not a single tool is not at odds with the need to consolidate capabilities. For example, you should not need to implement one solution to access internal applications and another for external applications. Look for solutions that integrate logically connected capabilities. This will simplify rollout and reduce operational complexity.
For the sake of this blog, I have assumed that data encryption, integration between various security components (like SIEMs, EDR/MDR, SSO), scalability, reliability and ease of deployment have become table stakes. My focus has been on elements that have evolved rapidly, not on requirements that have persisted from the pre-cloud era.
Share your thoughts! Reach out to us and let us know what you think - especially if you disagree, we want to hear from you! Send an email to info@appaegis.com or submit your comments by clicking here.
- Flexeral 2021 State of the Cloud Report
- Imperva Lessons learned from analyzing 100 data breaches
